Gatekeeper & Policies
OPA Gatekeeper is a policy enforcement engine for Kubernetes. SRExpert provides a visual interface to create, manage, and monitor Gatekeeper policies across your clusters.
Prerequisites
Before creating Gatekeeper policies, you need to install the Gatekeeper Helm Chart in your cluster.
Installing Gatekeeper
- Navigate to Helm Charts in the sidebar
- Select the Custom tab
- Find the gatekeeper chart
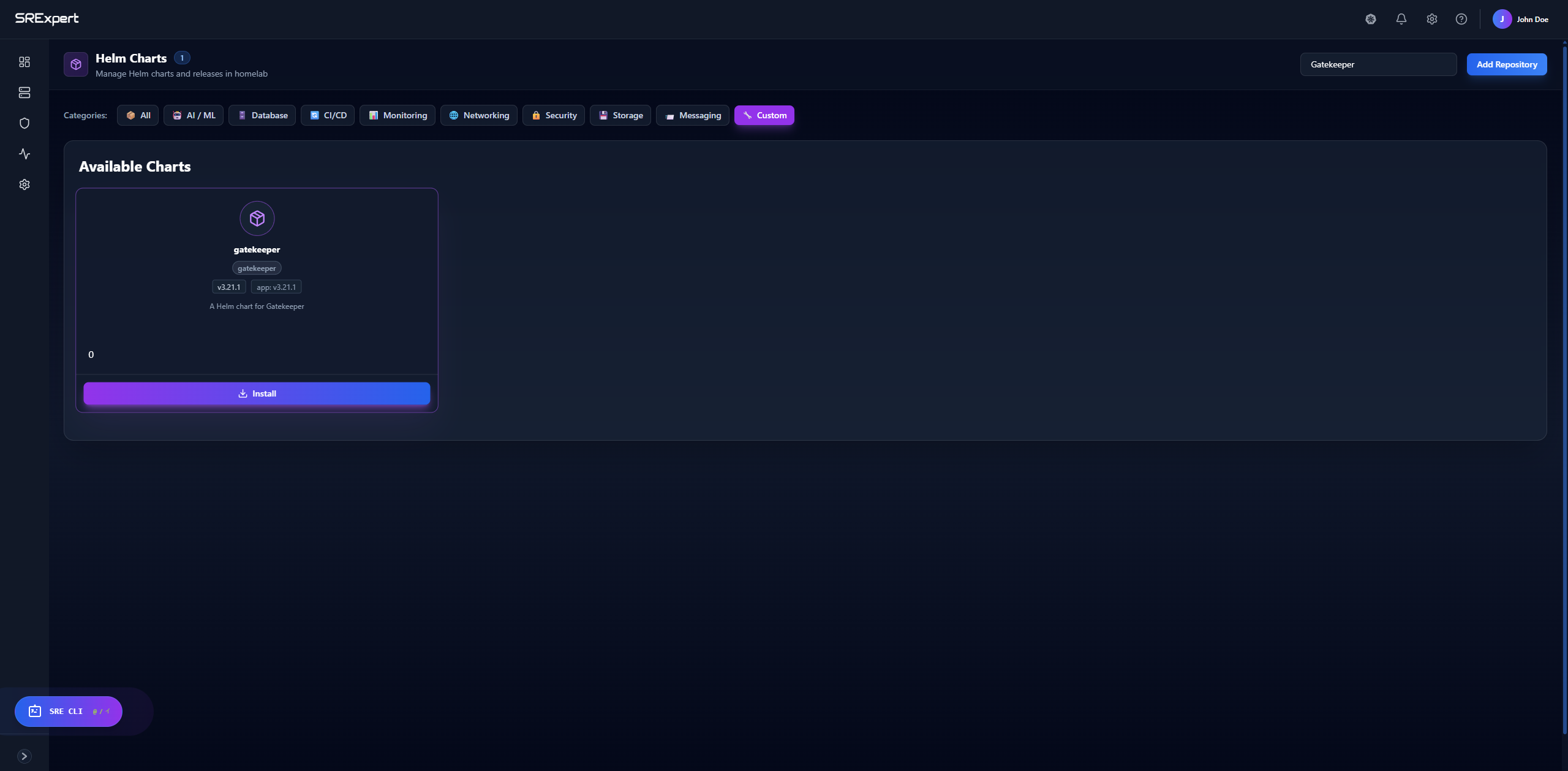
- Click Install and configure with default values (or customize as needed)
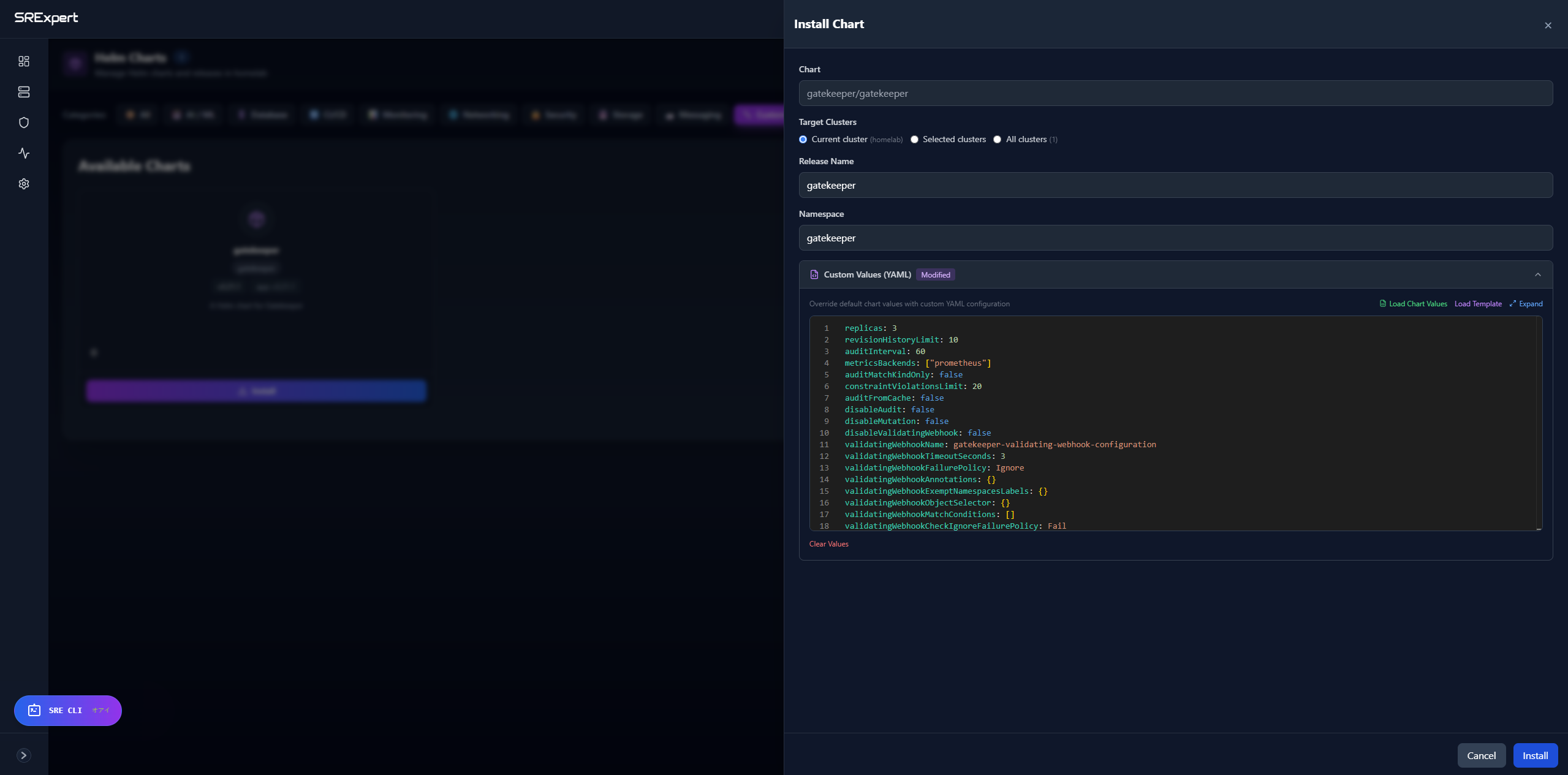
- Wait for the installation to complete. The Gatekeeper pods will be deployed in the
gatekeepernamespace.
Overview
Once Gatekeeper is installed, navigate to Security > Gatekeeper to access the policy management interface.
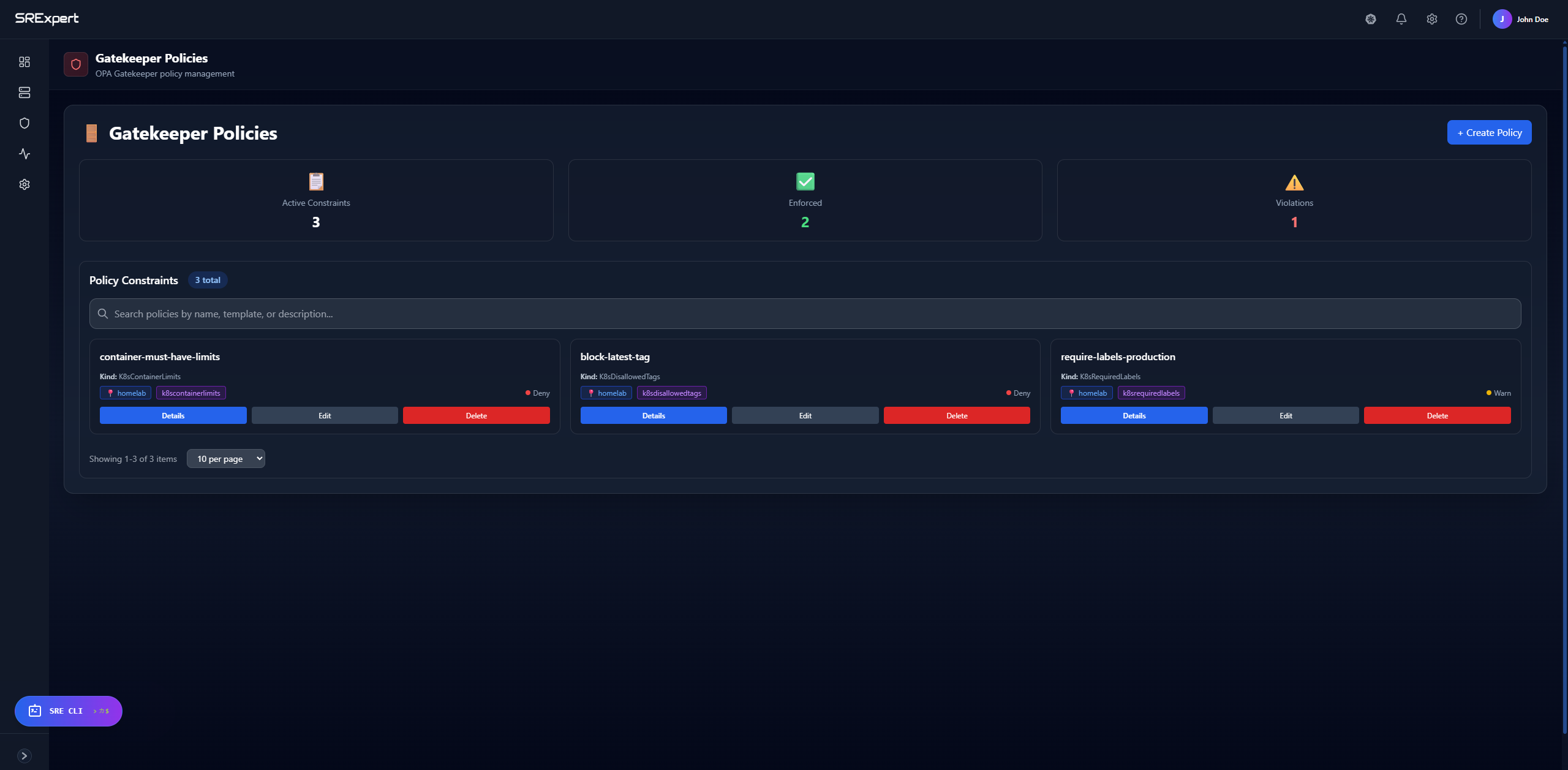
Gatekeeper uses Constraint Templates to define reusable policy logic and Constraints to apply those policies to your clusters. SRExpert simplifies this process with a visual interface that lets you:
- View all active policies and their status
- Monitor policy violations in real-time
- Create new policies from pre-built templates
- Edit and delete existing policies
Dashboard Metrics
At the top of the Gatekeeper view, you’ll see three key metrics:
| Metric | Description |
|---|---|
| Active Constraints | Total number of policies currently deployed |
| Enforced | Policies that block non-compliant resources (Deny mode) |
| Violations | Resources that violate your policies |
Managing Policies
Viewing Policies
Each policy card displays:
- Name: The constraint name (e.g.,
require-labels-production) - Kind: The constraint template type (e.g.,
K8sRequiredLabels) - Clusters: Which clusters the policy applies to
- Enforcement:
Warn(log only) orDeny(block)
Actions available:
- Details: View full policy configuration
- Edit: Modify policy settings
- Delete: Remove the policy
Viewing Violations
Click on a policy card or go to the Violations tab to see:
- Which resources are violating the policy
- The specific violation message
- Namespace and resource type
- When the violation was detected
Creating a Policy
Click + Create Policy to open the creation form.
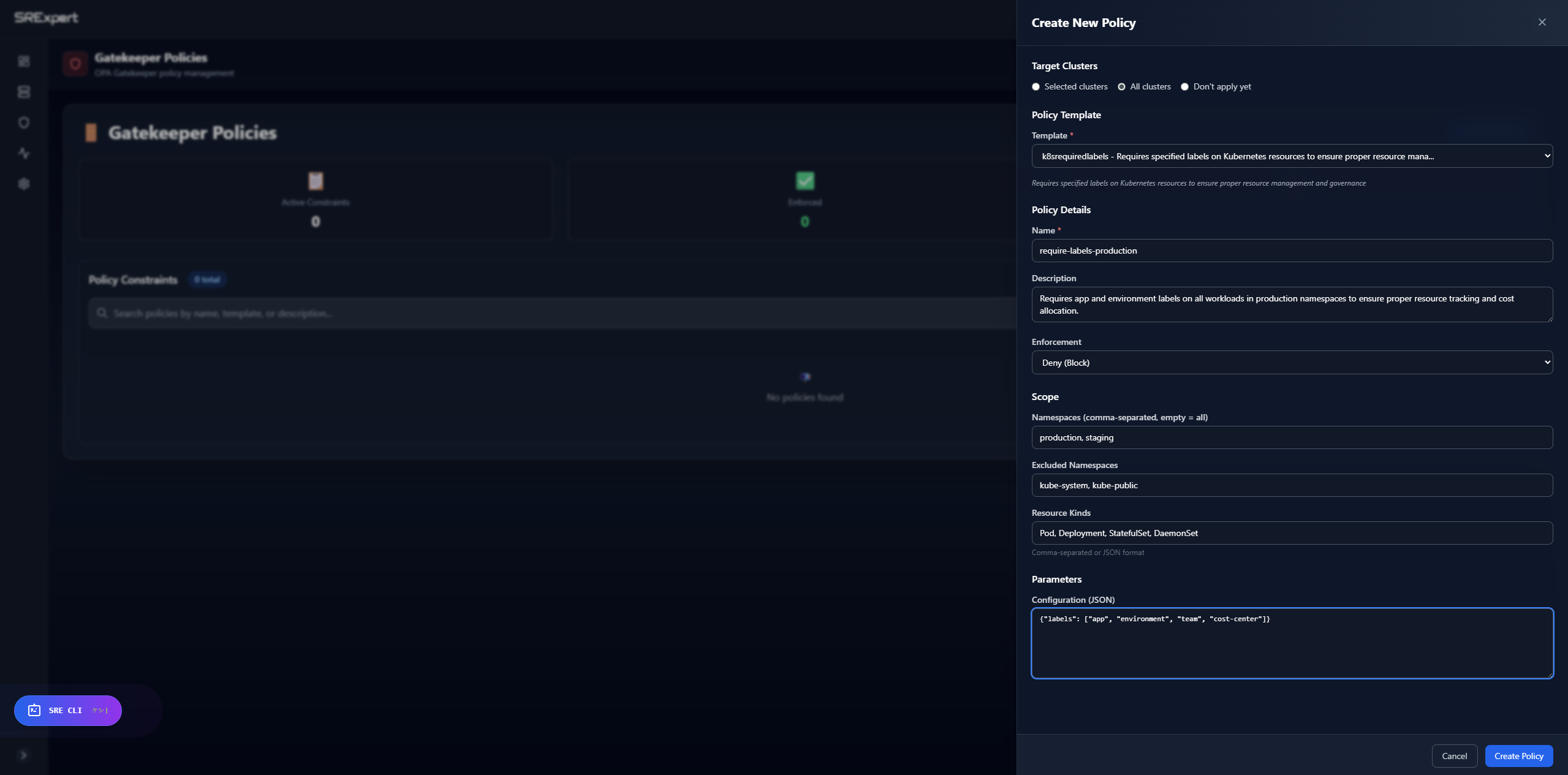
Step 1: Target Clusters
Choose where to apply the policy:
- Selected clusters: Pick specific clusters from the dropdown
- All clusters: Apply to every connected cluster
- Don’t apply yet: Save the policy without deploying
Step 2: Policy Template
Select a pre-built template from the dropdown. Common templates include:
| Template | Purpose |
|---|---|
K8sRequiredLabels | Require specific labels on resources |
K8sContainerLimits | Require CPU/memory limits on containers |
K8sAllowedRepos | Restrict container images to approved registries |
K8sDisallowedTags | Block specific image tags (e.g., latest) |
K8sBlockLoadBalancer | Prevent LoadBalancer service creation |
K8sBlockNodePort | Prevent NodePort service creation |
K8sHttpsOnly | Require HTTPS for ingress resources |
Step 3: Policy Details
- Name: A unique identifier for the constraint (e.g.,
require-labels-production) - Description: Explain what this policy enforces
- Enforcement:
Warn (Log only)- Log violations but allow the resourceDeny (Block)- Block non-compliant resources from being created
Step 4: Scope
Define which resources the policy applies to:
- Namespaces: Comma-separated list (empty = all namespaces)
- Excluded Namespaces: Namespaces to skip (e.g.,
kube-system, kube-public) - Resource Kinds: Which resource types to check (e.g.,
Pod, Deployment, StatefulSet)
Step 5: Parameters
Configure template-specific parameters in JSON format. For example:
K8sRequiredLabels:
{
"labels": ["app", "environment", "team"]
}K8sAllowedRepos:
{
"repos": ["gcr.io/", "docker.io/", "quay.io/"]
}K8sDisallowedTags:
{
"tags": ["latest", "dev"]
}Editing and Deleting Policies
- Click Edit on any policy card to modify its configuration
- Click Delete to remove a policy (this will stop enforcement immediately)
Best Practices
- Start with Warn mode: Test policies in warning mode before switching to Deny
- Exclude system namespaces: Always exclude
kube-systemandkube-public - Use descriptive names: Make policy names clear and searchable
- Monitor violations: Regularly check the dashboard to catch policy violations
- Document your policies: Use the description field to explain the policy’s purpose
- Apply incrementally: Start with a few critical policies and expand over time