Network Policies
Visualize and manage network traffic between pods in your cluster.
Overview
Network Policies features:
- Traffic visualization
- Policy management
- Topology view
- Traffic analysis
What are Network Policies?
Network Policies control traffic flow between pods:
- Default: All pods can communicate with each other
- With policies: Traffic is restricted based on rules
Note: Network Policies require a CNI that supports them (Calico, Cilium, Weave, etc.)
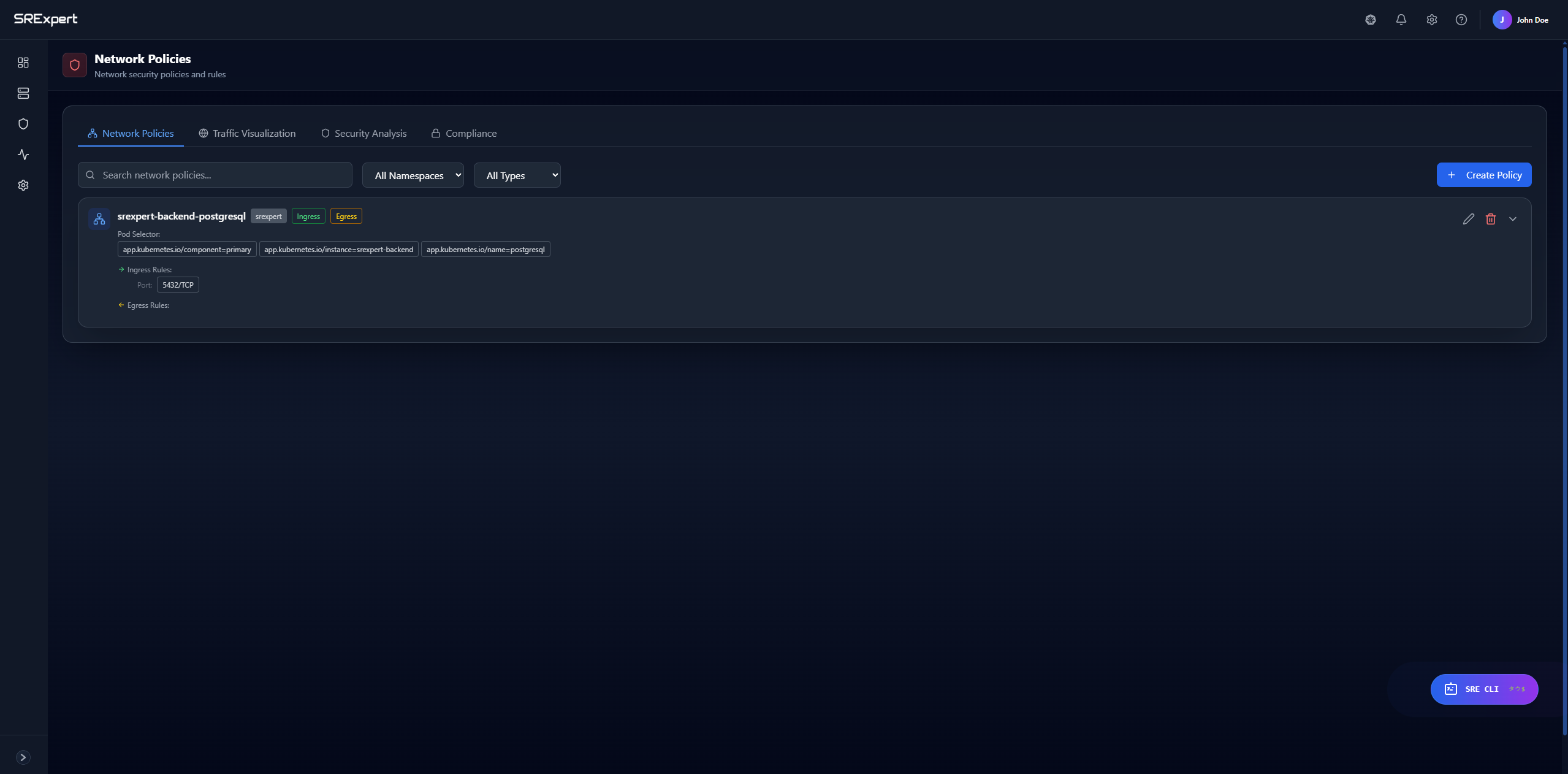
Viewing Policies
Policy List
Go to Security > Network Policies to see:
| Column | Description |
|---|---|
| Name | Policy name |
| Namespace | Applied namespace |
| Pod Selector | Affected pods |
| Ingress Rules | Inbound traffic rules |
| Egress Rules | Outbound traffic rules |
Policy Details
Click a policy to see:
- Full YAML specification
- Matched pods
- Traffic allowed/denied
Network Topology
Visualization
The topology view shows:
- Pods as nodes
- Connections as edges
- Allowed traffic (green)
- Blocked traffic (red)
Interactive Features
- Zoom in/out
- Click nodes for details
- Filter by namespace
- Search for pods
Creating Policies
Using the Wizard
- Go to Security > Network Policies
- Click New Policy
- Follow the wizard:
Step 1: Basic Info
- Name
- Namespace
- Description
Step 2: Pod Selector
- Select pods to apply policy to
- Use labels for selection
Step 3: Ingress Rules
- Who can send traffic to these pods
- Which ports are allowed
Step 4: Egress Rules
- Where can these pods send traffic
- Which ports are allowed
- Review and create
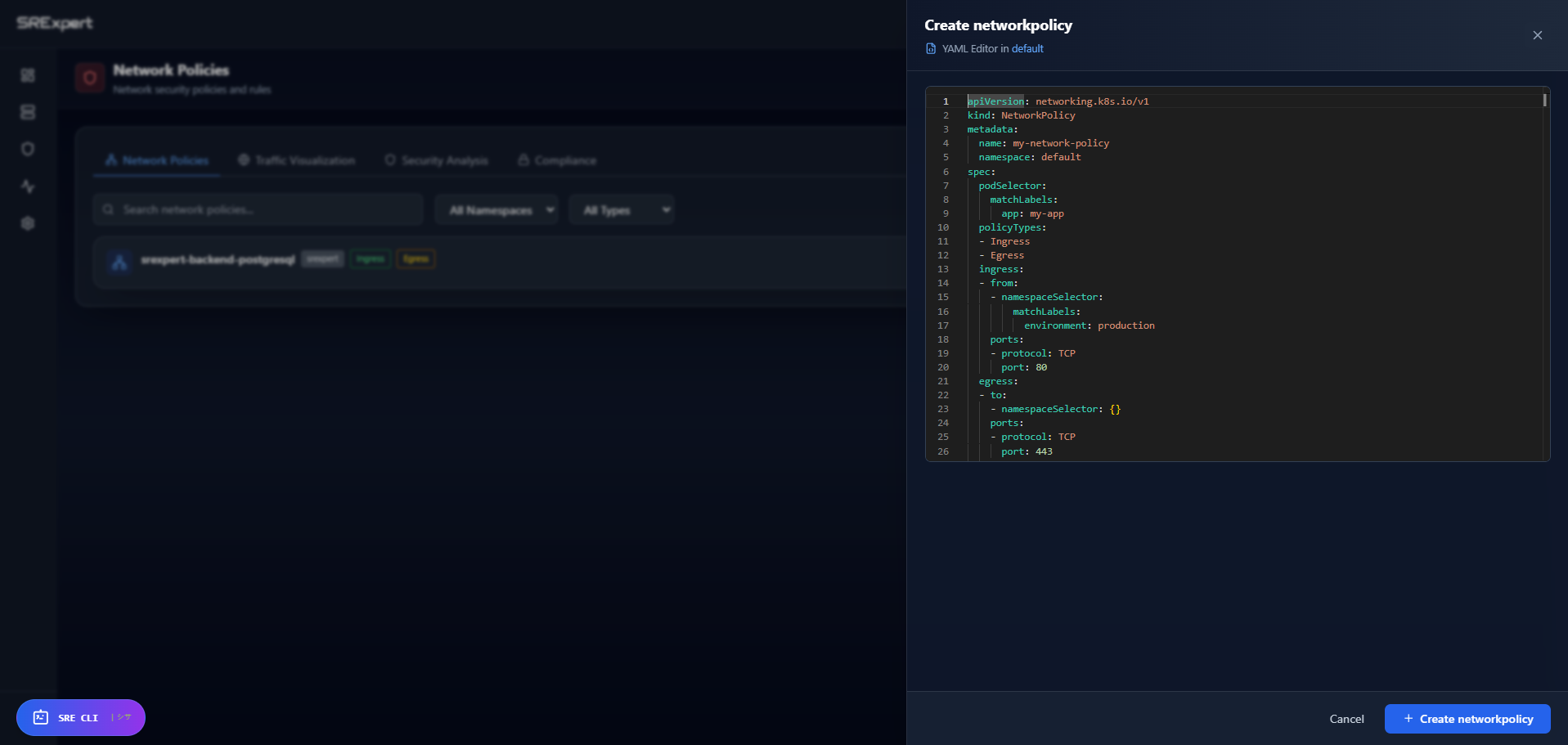
Using YAML
Create directly from YAML:
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: allow-frontend
namespace: production
spec:
podSelector:
matchLabels:
app: backend
policyTypes:
- Ingress
ingress:
- from:
- podSelector:
matchLabels:
app: frontend
ports:
- protocol: TCP
port: 8080Common Patterns
Deny All Traffic
Block all traffic by default:
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: deny-all
spec:
podSelector: {}
policyTypes:
- Ingress
- EgressAllow Same Namespace
Allow traffic within namespace only:
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: allow-same-namespace
spec:
podSelector: {}
ingress:
- from:
- podSelector: {}
policyTypes:
- IngressAllow from Specific Namespace
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: allow-from-monitoring
spec:
podSelector: {}
ingress:
- from:
- namespaceSelector:
matchLabels:
name: monitoring
policyTypes:
- IngressAllow DNS
Allow DNS resolution (usually needed):
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: allow-dns
spec:
podSelector: {}
egress:
- to:
- namespaceSelector: {}
ports:
- protocol: UDP
port: 53
policyTypes:
- EgressImpact Analysis
Before applying a policy:
- Click Analyze Impact
- See affected pods
- View connections that will be blocked
- Identify potential issues
Traffic Monitoring
Real-time Traffic
View live traffic flow:
- Source and destination
- Bytes transferred
- Connection status
Historical Data
Analyze past traffic patterns:
- Traffic volume over time
- Top connections
- Blocked attempts
Policy Testing
Dry Run
Test policies before applying:
- Create policy in draft mode
- Run simulation
- See predicted impact
- Apply or modify
Audit Mode
Apply policy in audit mode:
- Policy is active
- Violations are logged
- Traffic is not blocked
Troubleshooting
Policy Not Working
- Verify CNI supports Network Policies
- Check pod labels match selectors
- Ensure policy is in correct namespace
Pods Can’t Communicate
- Check if a deny-all policy exists
- Verify ingress/egress rules
- Use the topology view to debug
DNS Not Working
- Add egress rule for DNS (port 53)
- Check kube-system namespace access
Best Practices
- Start with deny-all - Add explicit allows
- Allow DNS first - Most apps need it
- Test in staging - Before production
- Use namespaces - Logical separation
- Document policies - Use descriptions
Next Steps
- Security View - Security overview
- Gatekeeper & Policies - OPA policies
- Troubleshooting - Debug issues